IBM AS/400 (also known as IBM iSeries) is approaching its 30th birthday. The system released in 1988 is still alive today and widely used across industries all over the world. Do you use AS/400 at your company? Have you been thinking of scaling up the security? Do you want to use SSL protocol to secure connection to AS/400 system and its DB2 database? Establish Secure Connection to IBM AS/400 in few steps with the help of CloverDX. All the necessary steps are described in the article below.
What is AS400 Database?
The AS400 database is the structured collection of records or data on IBM's AS400 server. It is a midrange server designed for small businesses and departments in large enterprises, and now redesigned so that it will work well in distributed networks with Web applications. Realizing the importance of compatibility with the thousands of programs written in legacy code, IBM launched the AS/400 midrange computer line in 1988.
Prerequisites
- The instructions below are for the most common CloverDX Server setup – UN*X operating system and application container Tomcat.
- The configuration can’t be done without an existing SSL certificate installed on the AS/400 server side. This is the only piece of work required on the server side. All the rest is done on the client side.
- JDBC driver must be used by CloverDX Server to access the remote DB2 database. There are two JDBC drivers available – native IBM Toolbox for Java and an alternate open source version called JTOpen. Both tools are maintained by the same development team, however the open source version is updated more frequently. We tested the solution on the open source version.
Database connections in CloverDX There are two ways to connect with a database in CloverDX. Using a
JDBC driver together with generic database components (
DatabaseReader,
DatabaseWriter,
DBExecute), or using one of our bulk writers component (
DB2BulkWriter). For our task using JDBC driver would be the correct method.
Configuration steps
All configuration steps described below are done on AS/400 client running instance of CloverDX Server.
1. Import your AS/400 SSL certificate into your truststore
First we need to import DB2 server's certificate into our truststore file, then configure CloverDX Server to use this truststore. We will use the Keytool utility to do this job. Command will look like this.
keytool -import -file cert.arm -alias as400_clovercert -keystore CATALINA_HOME/security/CloverTrustStore
It will create a new truststore called CloverTrustStore in $CATALINA_HOME/security folder and import the certificate from cert.arm file into a new key called as400_clovercert.
The system will asks two times for a new TrustStore password. Choose one according to your preference. Once the password is set, the system asks you if the imported certificate can be trusted. Type “yes” and press <Return>.
CATALINA_HOME is a system variable and its value can be found on “Environment properties” under Configuration > System Info section of CloverDX Server.
Note: You don't have to create a separate truststore for the CloverDX application. You can import the key into a default truststore located under JAVA_HOME/jre/lib/security/cacerts. In this case, the imported certificate would be available for all applications using the specified Java installation.
2. Grant access to your new truststore
Now you need to grant "read" access to the truststore for the users running CloverDX Server instance so they are able to utilize the certificate while using the JDBC connection.
3. Set path to your new truststore
Note: This step is not required if certificate had been imported into the default truststore.
In this step we will tell CloverDX where our new truststore is located. To do this, we need to amend the configuration file which passes JAVA_OPTS parameters to our CloverDX Server during the startup. If we have installed the CloverDX all-in-one bundle, the file is called setenv.sh (or setenv.bat) and is located under CATALINA_HOME/bin/ directory. If we are running a custom installation, the file is located under the application container configuration directory and the file name may be different.
Once we have located the file, following text should be added at the end of JAVA_OPTS definition.
# CloverDX connections certificate truststore
JAVA_OPTS="$JAVA_OPTS -Djavax.net.ssl.trustStore=<path to our new truststore>"
If you want to check an integrity of your TrustStore before the connection is established, provide also your TrustStore password. However this step is not necessary.
JAVA_OPTS="$JAVA_OPTS -Djavax.net.ssl.trustStorePassword=<your TrustStore password>"
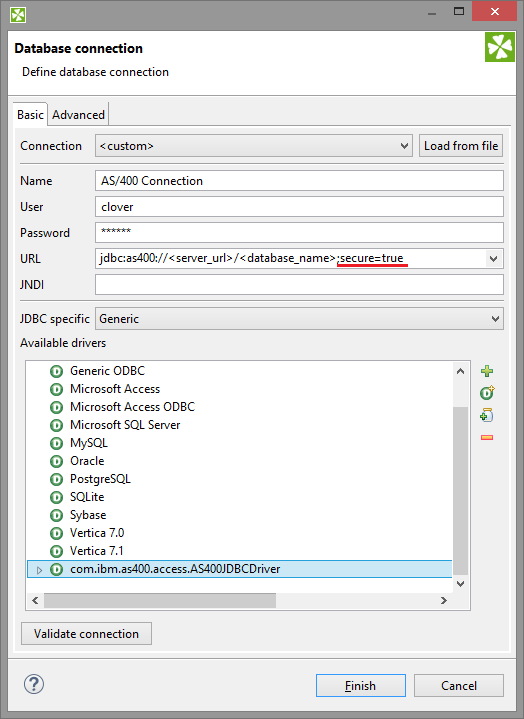
4. Modify your database connection
Almost there. The last step is the database connection definition. All we need to do is to set the parameter secure=true to encrypt all communication between server and client. Beside the encryption of connection, the SSL certificate will be used to authenticate the server.
When you use a JNDI connection type, navigate to your JNDI definitions and modify your AS/400 database connection as follows.
<Resource
name="jdbc/<your connection name>"
auth="Container"
type="javax.sql.DataSource"
driverClassName="com.ibm.as400.access.AS400JDBCDriver"
url="jdbc:as400://<server URL>/<database name>;secure=true"
username="<username>"
password="<password>"
maxActive="100"
maxIdle="20
validationQuery="select 1 from sysibm.sysdummy1"
testWhileIdle="true"
timeBetweenEvictionRunsMillis="300000"
maxWait="10000"/>
If you are using standard JDBC connection, your definition might look like this:
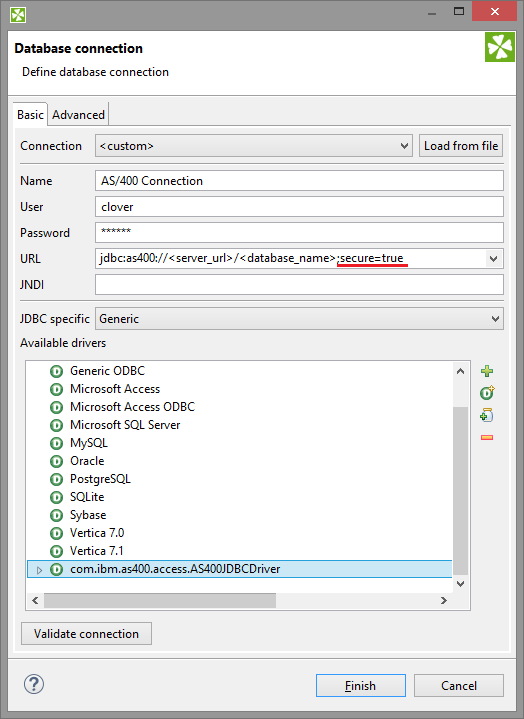
As a security precaution, you may want to prevent the ETL developers from knowing the database passwords required for the JDBC configuration. We keep this in mind during CloverDX development and offer the user options to secure their database passwords. You can protect your passwords using a
CloverDX Secure Parameters.
Conclusion
We managed to secure our AS/400 database connection in four easy steps which took no more than 30 minutes to complete. There are lots of rumours about the AS/400 platform circling within the IT community regarding the difficulties of integrating tools from different eras of computing. However, you can be at ease for this configuration is smooth and easy. As security continues to play a big role in data processing, it’s good to know that CloverDX can help you to cope with security challenges in such a convenient manner.